I'm quite surprised that an issue this big has so little conversation around it.
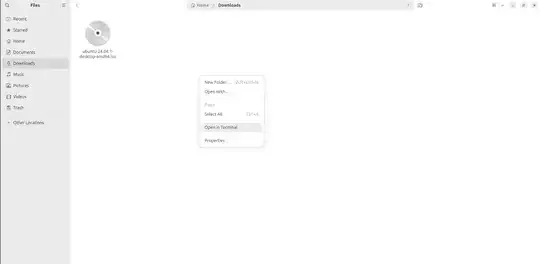
I'm a casual Ubuntu user, and I just downloaded the ISO from ubuntu.com.
I don't have a PGP web-of-trust set up on my computer or anything.
So the only thing I can really trust is my browser's CA list.
How would I go about verifying I'm not getting MITM'd and rootkit-level pwnd by a 16 y.o.? (Because it really is that easy)
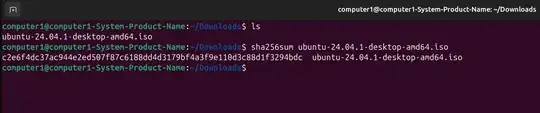
1. Just check the SHA256SUM
Well, unfortunately http://releases.ubuntu.com/ is only served via HTTP.
In fact there's a "Won't Fix" closed bug report from 2013 where maintainers explicitly deny bothering with providing users an HTTPS version of the hash list.
2. Just download Ubuntu's public keys with GPG
As mentioned in the VerifyIsoHowTo page, the other way to verify the download is to download Ubuntu's public key and verify the .gpg hash files.
However, in fine print, near the bottom it mentions something about building a web of trust. If we are to expand on that, I think we can safely state that checking the PGP signatures without a good web-of-trust in place is completely useless.
So what's left? Literally nothing. Of course you can spend a great deal of time trying to understand PGP, contacting colleagues and building your own web-of-trust over the following weeks, or you can just skip all that and just finally get on with the installation, which is what the crushing majority of people will do, if they even bothered getting that far.
So, is there a practical way for the casual/intermediate user to check the integrity of Ubuntu software prior to installing it, or are we wasting thousands upon thousands of man-hours to write secure code only to serve it insecurely?